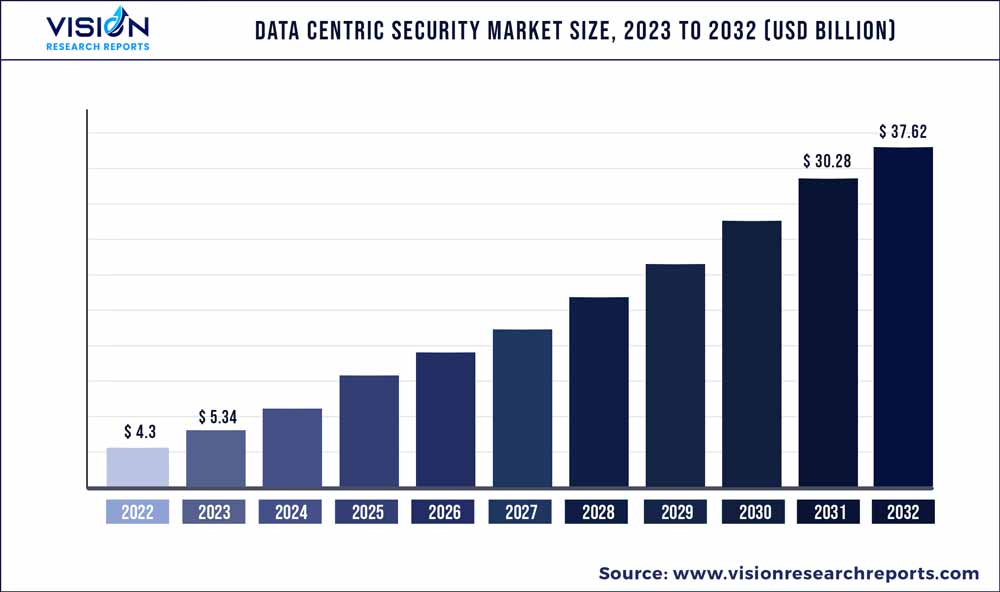
The global data centric security market size was estimated at USD 4.3 billion in 2022 and it is projected to hit around USD 37.62 billion by 2032, growing at a CAGR of 24.22% from 2023 to 2032. The data centric security market in the United States accounted for USD 1166.8 million in 2022.
Key Pointers
Report Scope of the Data Centric Security Market
| Report Coverage | Details |
| Revenue Share of North America in 2022 | 36% |
| CAGR of Asia Pacific from 2023 to 2032 | 26.53% |
| Revenue Forecast by 2032 | USD 37.62 billion |
| Growth Rate from 2023 to 2032 | CAGR of 24.22% |
| Base Year | 2022 |
| Forecast Period | 2023 to 2032 |
| Market Analysis (Terms Used) | Value (US$ Million/Billion) or (Volume/Units) |
| Companies Covered | Egnyte; Forcepoint; IBM; Imperva; Infogix; Informatica; McAfee; Micro Focus; Microsoft; NetApp; Netwrix; Orange Cyberdefense; Seclore; Symantec (now NortonLifeLock); Thales eSecurity; Varonis |
The growing amount of data being stored and used for regular operations across various locations of businesses has emerged the need for a data-centric security approach to protect the datasets. The increasing importance of data centric security across organizations is mainly due to the insufficient security across network servers and business applications and the need to secure sensitive information shared by the administrator to the users across the organizations.
Network servers and enterprise applications have inherent security vulnerabilities, making the highly secured network subjected to internal threats. Employees accessing the organization’s databases and systems can share confidential access or data with other employees. However, they are not directly related to their external parties or job duties, having no authorized access, thereby expanding the threat of data spill.
This possibility of threat increases with deploying a hybrid environment across organizations where employees work remotely or in the cloud. This emerges the need for direct data protection to form more barriers that repel unauthorized data distribution. Data centric security technology secures data from threats attacking confidential information, sensitive data, and employee errors, which can be stolen or leaked by unauthorized parties.
Further, data centric is essential for dynamic data protection, as it helps businesses gain more flexibility in managing the networks and systems compared to traditional access controls. Implementing the least privileged access among organizations allows the administration only to provide the user access to sensitive information of their files without providing them complete access to every other data on the server. This framework is effective when access to different functional data within the department is prohibited to the user.
Moreover, data centric security must be layered on top of existing systems to avoid additional large-scale changes. It is required for companies to restructure their privacy policies with the evolution of their security landscape to create strong authentication and encryption approaches. The data centric security technology enables the organization to protect the company’s data from cyber threats and increase the availability of resources for other purposes.
The technology helps to protect data stored on hard disks, accessed, or manipulated by applications, and transmitted over the network. This benefit has enabled organizations to deploy data centric solutions across verticals, thereby driving the demand.
However, most organizations need to be aware of the importance of avoiding the vulnerabilities and risks associated with deploying data centric security solutions. This factor can hinder the growth of the market. Moreover, the high cost associated with implementing and deploying data centric security solutions can hamper the growth.
Some small & medium-sized organizations have budget constraints that make it difficult to deploy such security solutions. The need to invest in technology, infrastructure, and personnel skills makes the complete deployment process costlier, restraining the growth of the data centric security market.
Solution Insights
The software segment accounted for the largest market share of 64% in 2022. The growing cyberattacks and data breaches have enhanced the demand for the data centric security software market. High-profile incidents have made it essential for the industries such as BFSI, IT & telecom, and retail to deploy these software solutions. Further, the government's growing focus on strengthening data privacy and regulatory compliance across regions supports the segmental growth of the market.
The services segment is expected to grow at the fastest CAGR of 24.92% over the forecast period. The growing importance of implementing effective user access controls and assuring the safety and security of confidential and regulated information drives the demand for the data centric security services market. The data centric security services are essential to implement zero-trust, as it allows an organization to secure critical datasets in real-time and apply the least privileged access approach across different storages.
Deployment Insights
The on-premise segment accounted for a market share of 48% in 2022. Organizations with strict governance policies or highly regulated industries often prefer to control their data assets completely. The on-premise data centric security solution enables organizations to maintain their data within their physical infrastructure, providing complete control over data storage, access, and security. This is one of the factors expected to propel the demand for the on-premise data centric security market over the forecast period.
The cloud segment is expected to grow at a CAGR of 25.13% during the forecast period. The growing transfer of data storage to the cloud makes it vital for organizations to enhance their security methods, creating demand for the cloud-based data centric security market. Cloud-based data centric security solutions enable the organization to have strong access control, data masking, and encryption techniques to safeguard sensitive information. Further, the growing need for secured collaborations and data sharing within and across organizations over a cloud has fueled the demand for the cloud-based data centric security market.
Enterprise Size Insights
The large enterprise segment held the largest market share of more than 54% in 2022. The growing cyberattacks across large enterprises owing to huge data storage sets and resource access on these storage units have fueled the demand for the data centric security market. Cyberattacks' growing complexity and integrity have emerged in the need to deploy highly advanced cybersecurity approaches, such as data centric security solutions. These solutions give organizations enhanced visibility allowing them to monitor and enforce data protection policies effectively and detect and respond to security incidents timely.
The Small & Medium-sized Enterprise (SME) segment is expected to witness a CAGR of 24.82% during the forecast period. The growing awareness among small and medium enterprises to have strong cybersecurity approaches owing to the growing sophistication and complexity of cyber-attacks has propelled the demand for the data centric security market. The growing security attacks such as phishing, ransomware, and data breaches have made it essential for SMEs to secure their data assets and sensitive information by deploying data centric security solutions.
Vertical Insights
The BFSI segment accounts for the largest market share of 27% in 2022. The BFSI sector stores valuable and sensitive data, including personal information, financial details, and trade secrets. This makes the BFSI sector a prime suspect for cyberattacks. The growing sophistication and frequency of cyber threats have created a greater emphasis on deploying a robust data security approach, enhancing the demand for data centric security.
Further, deploying cloud infrastructure across the BFSI sector for improving scalability, operational efficiency, and cost-effectiveness has emerged with the possibility of introducing various security concerns. Overcoming this data privacy issue across cloud platforms is anticipated to generate huge demand for data centric security.
The IT & telecom segment is anticipated to register the highest CAGR of 26.92% from 2023 to 2032. The increasing data volumes and end-user companies’ focus on providing secured access to data to their clients are driving the segment’s growth. The industry players are focusing on introducing industry-specific solutions to improve their brand positioning and increase their revenue stream. For instance, in March 2023, Cisco Systems, Inc. announced to launch new data center in Chennai; with enhanced security especially for its telecommunication industry clients, creating a positive market outlook.
Regional Insights
North America dominated the data centric security market in 2022 and accounted for 36% market share. The growing cyberattacks on government agencies, corporation, key infrastructure projects, and the population is anticipated to generate huge demand for data security solutions. This constantly changing and complex cyber threat infrastructure of North America has emerged the need for data centric security. The presence of several players, such as Microsoft, IBM, McAfee, and others in North America is expected to boost the growth. Furthermore, stringent government regulations such as California Consumer Privacy Act (CCPA), and General Data Protection Regulation (GDPR) have formed demand for advanced cybersecurity solutions to avoid legal and financial consequences, thereby surging the demand.
Asia Pacific is anticipated to rise at the fastest CAGR of 26.53% over the forecast period. The growing adoption of digitalization, machine learning, AI, and the Internet of Things (IoT) across areas of India, Australia, South Korea, and China has resulted in forming huge data assets which are required to be secured from vulnerable threats and risks such as ransomware, malware, data breaches, and others To overcome the cyber issues, the government is also imposing laws and regulations, such as the Information Technology Act, 2000 (ITA, or IT Act) of India, Cybersecurity Act of Singapore, and Security of Critical Infrastructure Protection Act of Australia, which is further creating demand for the data centric security.
Data Centric Security Market Segmentations:
By Solution
By Deployment
By Enterprise Size
By Vertical
By Regional
Chapter 1. Introduction
1.1. Research Objective
1.2. Scope of the Study
1.3. Definition
Chapter 2. Research Methodology
2.1. Research Approach
2.2. Data Sources
2.3. Assumptions & Limitations
Chapter 3. Executive Summary
3.1. Market Snapshot
Chapter 4. Market Variables and Scope
4.1. Introduction
4.2. Market Classification and Scope
4.3. Industry Value Chain Analysis
4.3.1. Raw Material Procurement Analysis
4.3.2. Sales and Distribution Channel Analysis
4.3.3. Downstream Buyer Analysis
Chapter 5. COVID 19 Impact on Data Centric Security Market
5.1. COVID-19 Landscape: Data Centric Security Industry Impact
5.2. COVID 19 - Impact Assessment for the Industry
5.3. COVID 19 Impact: Global Major Government Policy
5.4. Market Trends and Opportunities in the COVID-19 Landscape
Chapter 6. Market Dynamics Analysis and Trends
6.1. Market Dynamics
6.1.1. Market Drivers
6.1.2. Market Restraints
6.1.3. Market Opportunities
6.2. Porter’s Five Forces Analysis
6.2.1. Bargaining power of suppliers
6.2.2. Bargaining power of buyers
6.2.3. Threat of substitute
6.2.4. Threat of new entrants
6.2.5. Degree of competition
Chapter 7. Competitive Landscape
7.1.1. Company Market Share/Positioning Analysis
7.1.2. Key Strategies Adopted by Players
7.1.3. Vendor Landscape
7.1.3.1. List of Suppliers
7.1.3.2. List of Buyers
Chapter 8. Global Data Centric Security Market, By Solution
8.1. Data Centric Security Market, by Solution, 2023-2032
8.1.1. Solutions
8.1.1.1. Market Revenue and Forecast (2020-2032)
8.1.2. Services
8.1.2.1. Market Revenue and Forecast (2020-2032)
Chapter 9. Global Data Centric Security Market, By Deployment
9.1. Data Centric Security Market, by Deployment, 2023-2032
9.1.1. Cloud
9.1.1.1. Market Revenue and Forecast (2020-2032)
9.1.2. On-premise
9.1.2.1. Market Revenue and Forecast (2020-2032)
Chapter 10. Global Data Centric Security Market, By Enterprise Size
10.1. Data Centric Security Market, by Enterprise Size, 2023-2032
10.1.1. Small and Medium-sized Enterprises
10.1.1.1. Market Revenue and Forecast (2020-2032)
10.1.2. Large Enterprises
Chapter 11. Global Data Centric Security Market, By Vertical
11.1. Data Centric Security Market, by Vertical, 2023-2032
11.1.1. BFSI
11.1.1.1. Market Revenue and Forecast (2020-2032)
11.1.2. Government and Public Sector
11.1.2.1. Market Revenue and Forecast (2020-2032)
11.1.3. Healthcare
11.1.3.1. Market Revenue and Forecast (2020-2032)
11.1.4. IT and Telecom
11.1.4.1. Market Revenue and Forecast (2020-2032)
11.1.5. Retail
11.1.5.1. Market Revenue and Forecast (2020-2032)
11.1.6. Others
11.1.6.1. Market Revenue and Forecast (2020-2032)
Chapter 12. Global Data Centric Security Market, Regional Estimates and Trend Forecast
12.1. North America
12.1.1. Market Revenue and Forecast, by Solution (2020-2032)
12.1.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.1.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.1.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.1.5. U.S.
12.1.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.1.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.1.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.1.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.1.6. Rest of North America
12.1.6.1. Market Revenue and Forecast, by Solution (2020-2032)
12.1.6.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.1.6.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.1.6.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.2. Europe
12.2.1. Market Revenue and Forecast, by Solution (2020-2032)
12.2.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.2.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.2.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.2.5. UK
12.2.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.2.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.2.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.2.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.2.6. Germany
12.2.6.1. Market Revenue and Forecast, by Solution (2020-2032)
12.2.6.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.2.6.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.2.6.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.2.7. France
12.2.7.1. Market Revenue and Forecast, by Solution (2020-2032)
12.2.7.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.2.7.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.2.7.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.2.8. Rest of Europe
12.2.8.1. Market Revenue and Forecast, by Solution (2020-2032)
12.2.8.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.2.8.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.2.8.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.3. APAC
12.3.1. Market Revenue and Forecast, by Solution (2020-2032)
12.3.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.3.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.3.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.3.5. India
12.3.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.3.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.3.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.3.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.3.6. China
12.3.6.1. Market Revenue and Forecast, by Solution (2020-2032)
12.3.6.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.3.6.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.3.6.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.3.7. Japan
12.3.7.1. Market Revenue and Forecast, by Solution (2020-2032)
12.3.7.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.3.7.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.3.7.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.3.8. Rest of APAC
12.3.8.1. Market Revenue and Forecast, by Solution (2020-2032)
12.3.8.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.3.8.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.3.8.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.4. MEA
12.4.1. Market Revenue and Forecast, by Solution (2020-2032)
12.4.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.4.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.4.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.4.5. GCC
12.4.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.4.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.4.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.4.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.4.6. North Africa
12.4.6.1. Market Revenue and Forecast, by Solution (2020-2032)
12.4.6.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.4.6.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.4.6.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.4.7. South Africa
12.4.7.1. Market Revenue and Forecast, by Solution (2020-2032)
12.4.7.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.4.7.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.4.7.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.4.8. Rest of MEA
12.4.8.1. Market Revenue and Forecast, by Solution (2020-2032)
12.4.8.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.4.8.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.4.8.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.5. Latin America
12.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.5.5. Brazil
12.5.5.1. Market Revenue and Forecast, by Solution (2020-2032)
12.5.5.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.5.5.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.5.5.4. Market Revenue and Forecast, by Vertical (2020-2032)
12.5.6. Rest of LATAM
12.5.6.1. Market Revenue and Forecast, by Solution (2020-2032)
12.5.6.2. Market Revenue and Forecast, by Deployment (2020-2032)
12.5.6.3. Market Revenue and Forecast, by Enterprise Size (2020-2032)
12.5.6.4. Market Revenue and Forecast, by Vertical (2020-2032)
Chapter 13. Company Profiles
13.1. Egnyte
13.1.1. Company Overview
13.1.2. Product Offerings
13.1.3. Financial Performance
13.1.4. Recent Initiatives
13.2. Forcepoint
13.2.1. Company Overview
13.2.2. Product Offerings
13.2.3. Financial Performance
13.2.4. Recent Initiatives
13.3. IBM
13.3.1. Company Overview
13.3.2. Product Offerings
13.3.3. Financial Performance
13.3.4. Recent Initiatives
13.4. Imperva
13.4.1. Company Overview
13.4.2. Product Offerings
13.4.3. Financial Performance
13.4.4. Recent Initiatives
13.5. Infogix
13.5.1. Company Overview
13.5.2. Product Offerings
13.5.3. Financial Performance
13.5.4. Recent Initiatives
13.6. Informatica
13.6.1. Company Overview
13.6.2. Product Offerings
13.6.3. Financial Performance
13.6.4. Recent Initiatives
13.7. McAfee
13.7.1. Company Overview
13.7.2. Product Offerings
13.7.3. Financial Performance
13.7.4. Recent Initiatives
13.8. Micro Focus
13.8.1. Company Overview
13.8.2. Product Offerings
13.8.3. Financial Performance
13.8.4. Recent Initiatives
13.9. Microsoft
13.9.1. Company Overview
13.9.2. Product Offerings
13.9.3. Financial Performance
13.9.4. Recent Initiatives
13.10. NetApp
13.10.1. Company Overview
13.10.2. Product Offerings
13.10.3. Financial Performance
13.10.4. Recent Initiatives
Chapter 14. Research Methodology
14.1. Primary Research
14.2. Secondary Research
14.3. Assumptions
Chapter 15. Appendix
15.1. About Us
15.2. Glossary of Terms
 Cross-segment Market Size and Analysis for
Mentioned Segments
Cross-segment Market Size and Analysis for
Mentioned Segments
 Additional Company Profiles (Upto 5 With No Cost)
Additional Company Profiles (Upto 5 With No Cost)
 Additional Countries (Apart From Mentioned Countries)
Additional Countries (Apart From Mentioned Countries)
 Country/Region-specific Report
Country/Region-specific Report
 Go To Market Strategy
Go To Market Strategy
 Region Specific Market Dynamics
Region Specific Market Dynamics Region Level Market Share
Region Level Market Share Import Export Analysis
Import Export Analysis Production Analysis
Production Analysis Others
Others